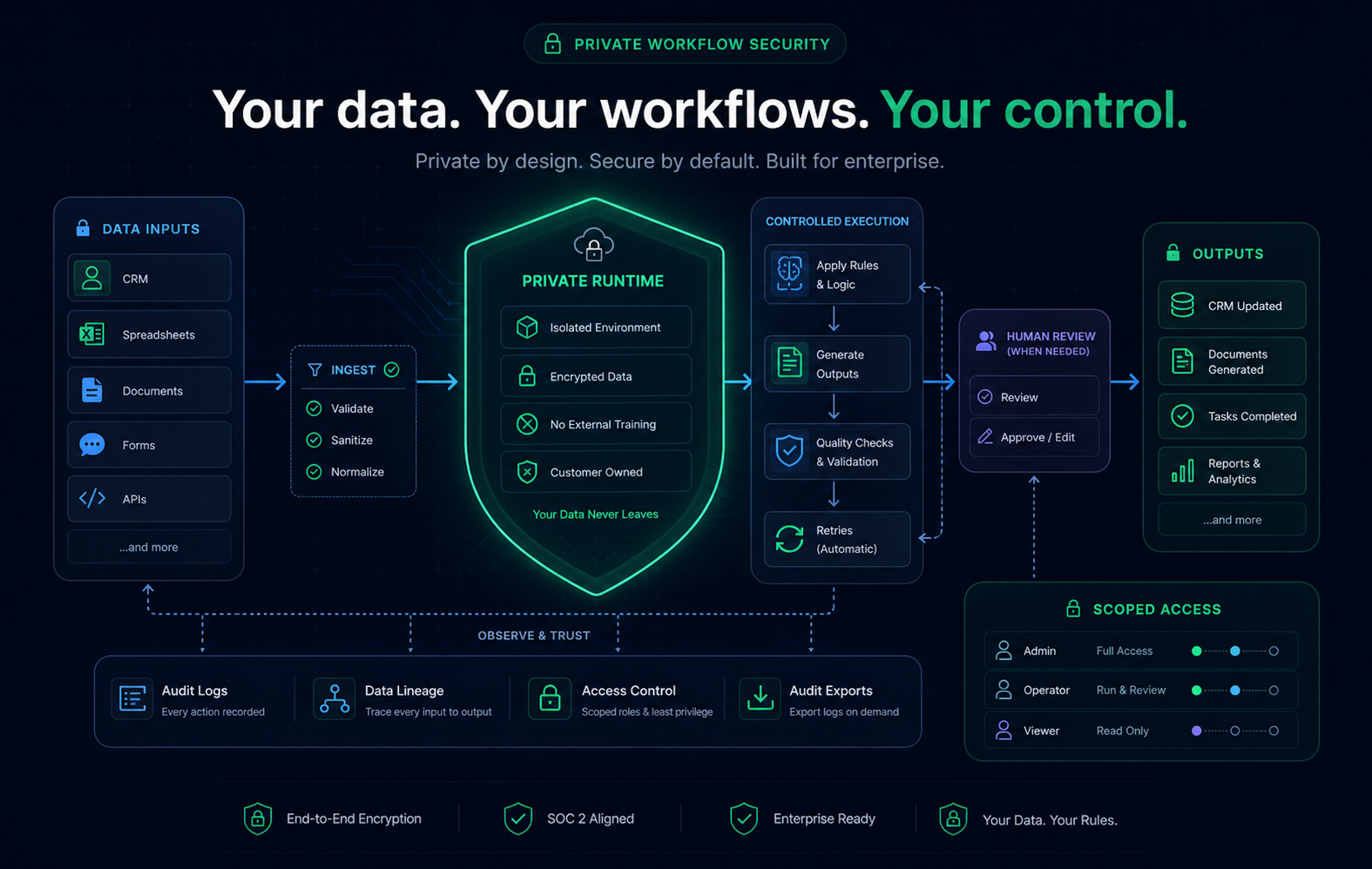
Private workflow automation security
For sensitive workflows, we prioritize running automation inside the client environment with logs, retries, and controlled data flow.
What this means
The workflow is designed around control, traceability, and minimal data movement.
Why it matters
Sensitive operations need more than a black-box tool with no operational visibility.
What we avoid
Loose integrations and blind data routing that are hard to audit.
How private automation is delivered
1. Scope
We map the workflow, inputs, approval points, and output format before any build starts.
2. Runtime
The automation runs inside your environment when needed, or in a tightly controlled hosted setup when approved.
3. Logging
Every run creates a traceable record so you can review inputs, outputs, and failures without guessing.
4. Recovery
Retries, approval steps, and human review gates are added where silent failure would be expensive.
Operational safeguards
- �Only the minimum fields required for the workflow are processed.
- �Retries are limited and visible, not hidden inside a black-box queue.
- �Human approval can be inserted before any external side effect happens.
- �We keep handoffs traceable so operations can audit what happened and when.
FAQ
Does all data leave my environment?
No. We favor private execution and only use external services when the workflow explicitly requires it.
What happens if a step fails?
Failures are logged and either retried or handed back to a human review step, depending on the workflow design.
Is this only for large teams?
No. Private automation is useful when the workflow is repetitive, sensitive, or expensive to do manually, regardless of team size.